Do you ever wonder how all these celebrities continue to have their private photos spread all over the internet? While celebrities' phones and computers are forever vulnerable to attacks, the common folk must also be wary. No matter how careful you think you were going you sent those "candid" photos to your ex, with a little effort and access to public information, your pictures can be snagged, too. Here's how.
Cloud Storage
Apple's iCloud service provides a hassle-free way to store and transfer photos and other media across multiple devices. While the commercial exemplifies the G-rated community of iPhone users, there are a bunch of non-soccer moms that use their iPhones in a more..."free-spirited" mindset. With Photo Stream enabled (requires OS X Lion or later, iOS 5 or later), pictures were taken on your iPhone go to directly to your computer and/or tablet, all while being stored in the cloud.
If you think the cloud is safe, just ask Gizmodo reporter Mat Honan. His iCloud account was hacked by someone who contacted Apple Support and requested a password reset by working around the security questions and using available information of Honan's social media accounts. The hacker remotely wiped all of Honan's devices and hijacked the Gizmodo Twitter account. Luckily for him, his photos were not of any concern to the hacker, but other people might not be so lucky.
That's how some "intriguing" photos of Scarlett Johansson ended up all over the internet last year. The hacker simply found her email address by trying random iterations of her name in combination with common email clients like Gmail or Yahoo, and then used the forgotten password helper. After answering the security questions by using public information and scouring the internet, he gained access to her email account, which contained some of her photos.
Once a hacker has an email address, the information he or she now has access to has multiplied. Many people prefer paperless billing for their obligations, cell phone bills included. On those cell phone bills is the number of the account holder as well as a ton of other information like outgoing and incoming calls. And if you are using Gmail, you can send text messages right inside the email client, making it even easier to get in touch with other contacts.
So, while email hacking might not get you to the images directly, it can lead you to various sources of information that will get you closer to your goal, like a cell phone number. With your target's cell phone number in hand, those photos are within reach.
Cellular Provider
Sometimes the cellular provider is the weakest point of defense for a cell phone user. Both AT&T and Verizon allow user ID's to be the customers wireless number. If you have the number of the phone, you can use the "forgot my password" feature to request for a temp password, or even change the password altogether by either entering a 4 digit pin code, crackable by brute force, or by answering a few security questions. Do you want free internet?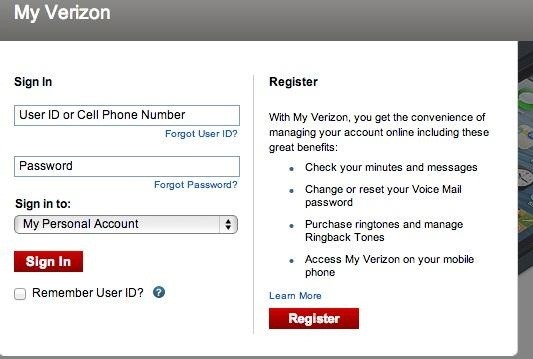
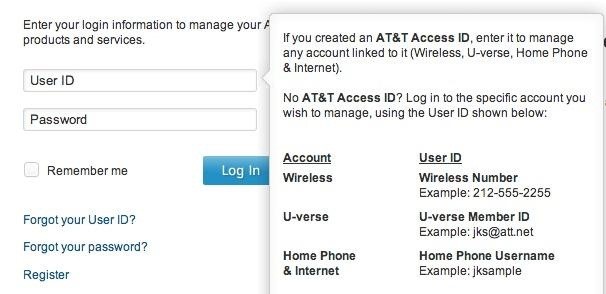
Studies have shown that most people are terrible at choosing PINs, so you may not even have to use brute force—just try the list of most common ones that people use. Once inside the account, you have access to all the usage and data the phone has sent or received in the latest billing period.
Spoofing
With access to the numbers a cell phone has contacted and access to the text messages that have been sent from it, it's not too hard to spoof someone's number. Instead of trying to steal the photos off the phone, you can trick them into sending them directly to you. There are a bunch of cell phone spoofs and Caller ID apps you can use to make your number appear to be someone else's.While none of these methods are guaranteed, there's a good chance that one of them (or a combination of a few) will work, unless your target is more security savvy than the average person. Most of us give away more information than we know online, and it only takes one opportunity-minded individual to take advantage of it.
If you do decide to give it a shot, though, just remember: hacking into someone's email or cell phone accounts is not only in the moral grey area, it's also completely illegal, so proceed with caution.

0 Comments